Businesses today strive to secure their company data through effective solutions that can mitigate risks and data breaches. With the increasing complexity and size of systems, access control creates a special concern when the systems are distributed among different computers across borders.
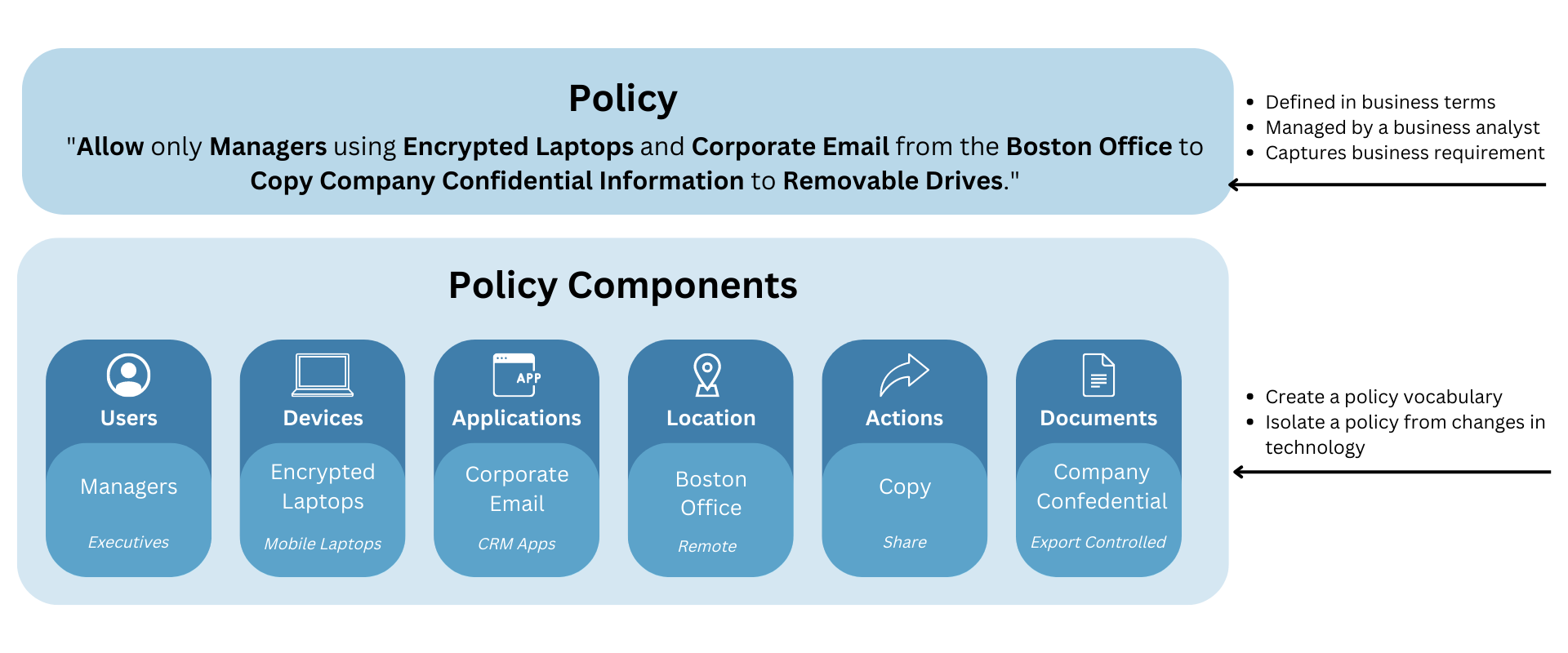
An access control system determines who or what can view or use resources in a computing environment. It is a fundamental concept in security that minimizes risks such as data breaches, wrongful disclosure, and fraud. Within the system lies the core communication structure which is the scripting or policy language used to specify access control policies. NextLabs’ Active Control Policy Language (ACPL) is a fourth-generation policy language (4GL) based on the XACML standard for access control that makes it easy for non-technical users to learn and understand. ACPL is made up of a set of subject and resource component definitions and grammatical rules to determine permissions and provide authorization instruction to perform specific tasks. ACPL’s natural-language syntax simplifies the way policy-based (PBAC) and attribute-based access control (ABAC) policies are authored and managed.
Made for Business Users – NextLabs’ Active Control Policy Language (ACPL)
NextLabs’ Active Control Policy Language is based on XACML (eXtensible Access Control Markup Language) which is an OASIS standard for access control designed for Attribute-Based Access Control (ABAC). It is both an access language, with a request/response interface and reference architecture. Policy language expresses the policies, such as who may access which files under which department.
In the past, policies were formulated by business users and implemented to the system by programmers. As a result, there is a lot of back and forth between business users and programmers. On the other hand, ACPL is a non-procedural language that uses natural language syntax, enabling non-technical users to write and manage their own policies, without requiring additional programming help, thereby increasing the efficiency of businesses. As a result, the unique combination of XACML and 4GL positions ACPL to be the industry standard going forward.
Key Highlights of ACPL
- Business Friendly: ACPL uses natural language for policy definition allowing business users to directly author policies without the need for technical resources.
- Simplicity: ACPL is simple to use without requiring technical knowledge. With the Policy Studio GUI, policy can be created in ACPL quickly. It takes very little time to learn, understand, and write ACPL policies.
- Reusability: ACPL is a component-based policy language, which means that subject, action, and resource components only need to be created once to then be used in all policies. These reusable components are also easy to understand and create.
How does ACPL benefit enterprises?
The main function of ACPL and its XACML framework is to enable the development of effective security policies across an entire enterprise, instead of implementing individual policies for each point of access. This enables a common language and interoperability of various access control implementations across applications.
With the evolution of identity access management, many enterprises have adopted single sign-on systems where web-based authentication and coarse-grained authorization logic are separated from applications. ACPL provides organizations a simple and easy way to manage an approach to implementing rich, fine-grained access control policies.
By simplifying the process of authoring and managing PABAC and ABAC policies, ACPL can improve upon an organization’s access control practices by allowing an enterprise to extend existing roles using attributes and policies. Authorization decisions can be made based not only on a user’s role but also by considering other factors such as, who, where, and what that user is related to, and the resource being accessed. Therefore, by using a simple, easy-to-understand policy that considers the context of the user as well as what access he/she should have, access control becomes stronger and grows significantly in scope.
By facilitating the adoption of PBAC and ABAC policies, ACPL also streamlines the management process for dynamic authorization. It removes the need to individually administer thousands or even hundreds of thousands of access control lists and/or role and role assignments on a daily basis. Additionally, organizations do not need to deploy expensive and complex identity governance solutions. With ACPL policies, hundreds of roles can be replaced by just a few policies. These policies are managed centrally across all sensitive applications and systems, providing a single pane of glass over the “who, what, where, when, and why.” Centralized management makes it easy to add or update policies and quickly deploy them across the enterprise.
Furthermore, many enterprises are now developing custom access control solutions to meet the complex needs of their business. However, this can be costly and make it difficult to maintain quality service. With ACPL, enterprises can avoid this dilemma entirely by adopting a commercial off-the-shelf (COTS) solution instead of building a custom one. The fine-grained, attribute-based nature of ACPL means, policies can be modified without requiring code changes or application downtime. This enables organizations to react quickly to changes in business or regulatory environments, greatly increasing agility and flexibility, and enhancing overall data protection while greatly reducing cost. Centralized access policies means it is not necessary to make software changes to individual applications to ensure consistent enforcement of policies across essential business applications.
The Underlying Language of NextLabs CloudAz
“Language is a system of systems” – ACPL runs through all the technology exposed through the platform’s user interfaces, being the language that makes everything possible in NextLabs’ CloudAz, our Zero Trust Policy Platform which is the backbone of NextLabs’ Data Centric Security product suite used to solve the most complex access and data protection challenges.
Since ACPL uses natural language for policy definition, it can be a common access control language between business and IT users. This allows business users to directly author policies without the need for technical resources.
NextLabs CloudAz is a centralized platform that enforces security policies consistently across the enterprise and beyond, integrating automated data classification, access control, rights management, and audit capabilities into one powerful platform that enables better alignment of policies with rapidly changing business requirements. The platform can be delivered either on-premises or in the cloud.
Using ACPL, CloudAz policies can be modified without requiring code changes or application downtime. This enables organizations to react quickly to changes in business or regulatory environments, greatly increasing agility and flexibility, and enhancing overall data protection. Dynamic authorization policy engine with the zero trust policy platform also allows for central monitoring and tracking of user activity and data access providing compliance and security officers with insight into user behavior and suspicious activities.
For more information on ACPL, read What is Active Control Policy Language (ACPL)?
Explore CloudAz, NextLabs’ unified policy platform with real-time enforcement which centralizes administration and employs a zero-trust strategy to enforce data-centric security (DCS) measures and compliance.





