Home | Intelligent Enterprise | Zero Trust Architecture | What is Zero Trust Architecture (ZTA)?
Zero Trust Architecture: The Foundation of Zero Trust Security
A traditional security model implicitly trusts everything inside an organization’s network, leaving plenty of loopholes for human error and insider threats. Zero trust security emerged to address these weaknesses by eliminating implicit trust entirely. This approach is no longer sufficient under today’s circumstances, as remote work, global teams, and hybrid cloud environments make network boundaries increasingly difficult to define. Given these challenges, it is becoming increasingly difficult to define network perimeters. Additionally, when subjects (end users, applications, non-person entities requesting information) are given broad access to resources within the network perimeter, the compromise of a single subject can snowball into massive data breaches. These challenges have driven organizations to adopt zero trust architecture (ZTA) as the structural foundation for implementing zero trust security at scale.
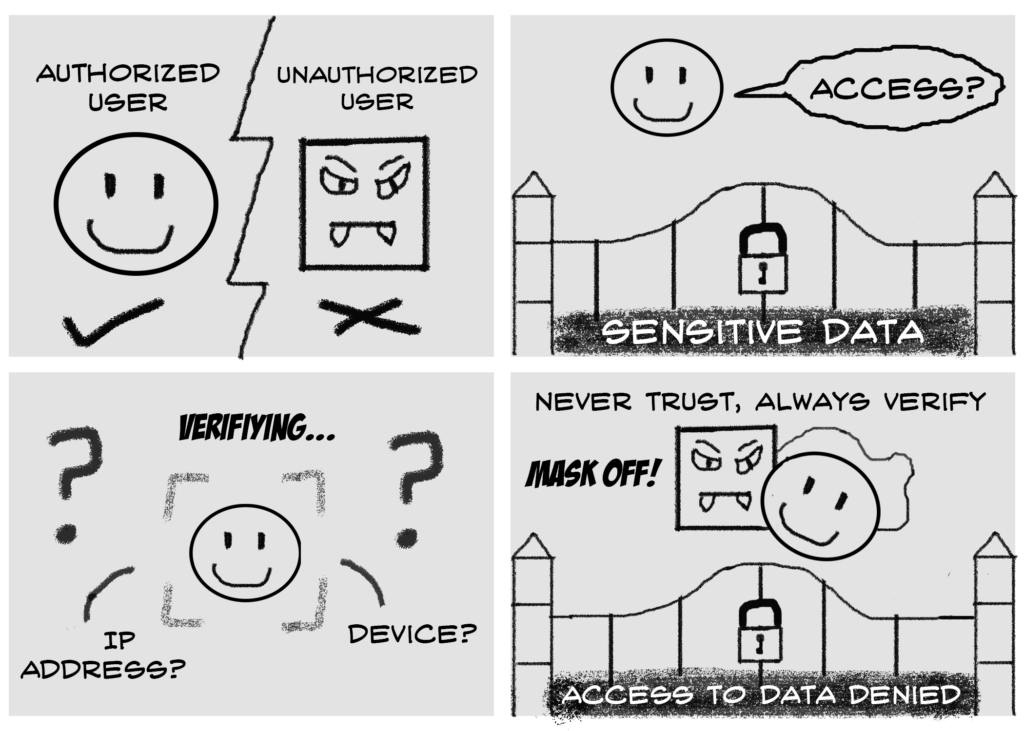
As defined by NIST, a ZTA employs a data-centric methodology that focuses on protecting resources rather than relying on a traditional network perimeter and serves as the architectural basis for zero trust security. Since the network perimeter is no longer the key component to safeguarding enterprise data, a zero-trust strategy shifts its line of sight to identifying and authenticating users and devices. Zero-trust encompasses a set of principles that safeguards subjects, enterprise assets, and resources. These principles include “never trust, always verify,” “assume breach,” and “least privileged access,” which collectively define how zero trust security is implemented within a ZTA.
ZTA, with its “never trust, always verify” principle, removes implicit trust from all subjects, even those operating within the network perimeter. This allows it to enforce more granular levels of security control. When every stage of a digital transaction is evaluated for authorization, users are less likely to overstep the boundaries of what they are allowed to access. This continuous verification model is a core requirement for effective zero trust security, ensuring that trust is never assumed at any stage of access.
By assuming that a data breach has already occurred, ZTA prepares organizations for worst-case scenarios and enables zero trust security controls to limit the impact of an attack when it does occur. This goes hand in hand with its principle of enforcing “least privileged access”, where users and applications are granted the least amount of access needed to complete their duties effectively.
Why Zero Trust Architecture?
When combined with dynamic, automated controls, ZTA enables enterprises to operationalize zero trust security while achieving regulatory compliance and balancing security, availability, usability, and cost efficiency.
In highly collaborative environments, ZTA’s enforcement of least-privileged access helps safeguard business-critical information and is a foundational control within zero trust security strategies. With real-time access control, users are reliably verified and authenticated before each session.
ZTA also allows organizations to better track and monitor patterns in user behavior, improving visibility across users, devices, and resources. With increased visibility over resources, enterprises can detect suspicious activity and protect data accordingly. Due to the absence of a “trusted” network and location, every connection is subjected to verification, reducing the overall risk of malicious attacks. When security events do happen, the simplified security architecture of ZTA allows enterprises to respond swiftly and effectively. This level of visibility is essential to maintaining continuous verification and enforcing zero trust security over time.
To learn more about ZTA and its role in enabling zero trust security, please refer to NextLabs’ interview with Alper Kerman, author of the Implementing a Zero Trust Architecture document, on Why is Zero Trust Architecture (ZTA) Important?





