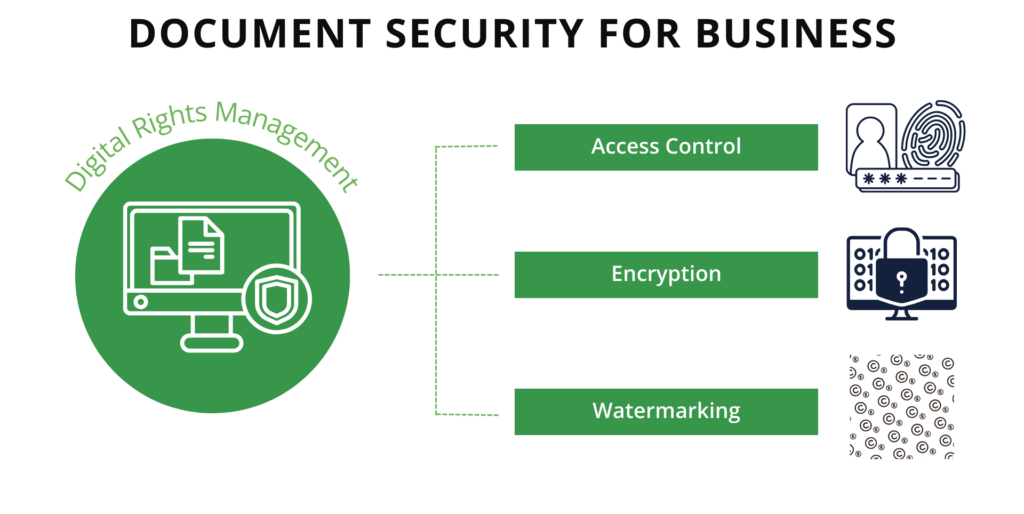
Sharing documents online is impossible to avoid in the workforce today. Whether a user is sharing documents within their department, across the extended enterprise, or with partners and joint ventures, maintaining a level of security on these shared documents is necessary.
Document security refers to measures taken to prevent data in documents from being wrongfully accessed, manipulated, or reproduced. Examples of document security measures include encrypting documents, controlling access to confidential information, and monitoring the use of documents and files. In addition, documents can be secured by restricting usage to prevent document damage, using secure computer systems and networks, and proper removal of unattended documents and records.
To comment on this post
Login to NextLabs Community
NextLabs seeks to provide helpful resources and easy to digest information on data-centric security related topics. To discuss and share insights on this resource with peers in the data security field, join the NextLabs community.
Don't have a NextLabs ID? Create an account.