In the attribute-based access control (ABAC) architecture, the policy information points (PIP) are the system entity that act as a source of attribute values.
ABAC, also known as policy-based access control for IAM, defines an access control paradigm whereby a subject’s authorization to perform a set of operations is determined by evaluating attributes associated with the subject, object, requested operations, and, in some cases, environment attributes.
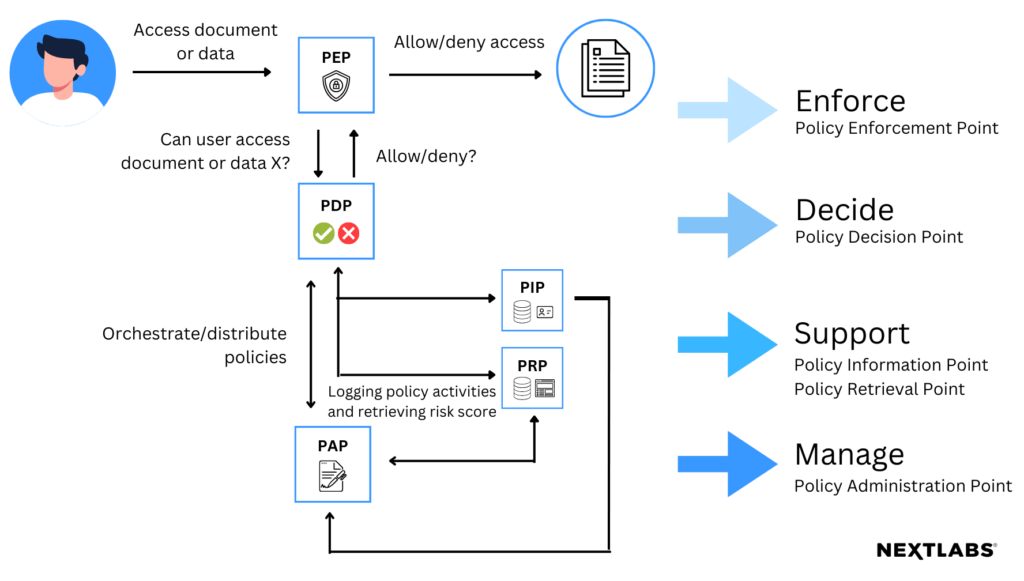
ABAC comes with a recommended architecture which is as follows:
- The PEP or Policy Enforcement Point is responsible for protecting the apps & data you want to apply ABAC to. The PEP inspects the request and generates an authorization request from which it sends to the PDP.
- The PDP or Policy Decision Point is the brain of the architecture. This is the piece which evaluates incoming requests against policies it has been configured with. The PDP returns a Permit/ Deny decision. The PDP may also use PIPs to retrieve missing metadata.
- The PIP or Policy Information Point bridges the PDP to external sources of attributes e.g. LDAP or databases.
- The PAP or Policy Administration Point feeds policy to the PDP. It provides a centralize depository to manage policy especially for the enterprise architecture.
How Does a Policy Information Point Work?
The primary function of a PIP is to supply real-time attribute information to the PDP during the access evaluation process. The PIP retrieves and provides the necessary attribute data, which may include user roles, resource properties, environmental conditions, and other contextual information. By interfacing with various data sources and repositories, such as directories, databases, or external systems, the PIP ensures that the PDP has up-to-date and accurate attribute information to make informed access control decisions. The dynamic nature of ABAC relies on the PIP to furnish the PDP with the current state of relevant attributes, contributing to the adaptability and precision of access control policies in response to changing conditions within an organization’s environment.
Why are PIPs Necessary?
The PIP is crucial in access control systems for several reasons. In complex security architectures, especially those employing ABAC, access decisions depend on a multitude of dynamic attributes related to users, resources, and the environment. The PIP serves as the source of real-time attribute information, providing the necessary data to the PDP during the decision-making process. Without the PIP, the PDP would lack the essential attribute details, leading to less precise and potentially outdated access control decisions, undermining the effectiveness of the overall security framework. Therefore, the PIP is indispensable in maintaining the integrity and responsiveness of access control systems.
To learn more about the other components of the ABAC architecture, read our previous blogs on PDP, PAP, and PEP.
To comment on this post
Login to NextLabs Community
NextLabs seeks to provide helpful resources and easy to digest information on data-centric security related topics. To discuss and share insights on this resource with peers in the data security field, join the NextLabs community.
Don't have a NextLabs ID? Create an account.