Centralize Policy Management with a Unified Zero Trust Policy Platform
NextLabs CloudAz enables companies to apply Zero Trust and Data-Centric Security principles with Attribute-Based Access Control to safeguard data and applications in hybrid clouds.


CloudAz Brochure
Explore the brochure on how to achieve a unified approach for access management and data security
BAE Customer Story
Learn how BAE complies with electronic export regulations and protect IP while enabling and accelerating global collaboration
CloudAz DataSheet
Discover why enterprises need a Zero Trust strategy for secure global data access and a virtual workforce without compromising integrity
The Need to Protect Data at the Source
01
Virtualized Workforce
Today's enterprises need a zero trust strategy to enable a virtual workforce without compromising sensitive data and business integrity.
02
Single Global Instance
The global workforce and business partners need to access data from anywhere in a way that is simple and secure.
03
Regulatory Landscape
A shifting geopolitical landscape has spawned regulatory complexities in managing digital enterprise resources.
04
Cloud Computing Paradigm
Adoption of cloud computing by enterprises necessitates a paradigm shift from network-centric security to data-centric security.
05
Evolution of Industries
Rapid industry change means a static approach to cybersecurity can't keep up with evolving security, privacy, and compliance requirements.
How can enterprises modernize IT, ensure compliance & protect data while reducing cost, complexity & breaches?
The Solution:
It is inevitable for enterprises to progress from silos toward a unified approach for access management and data security.

What does a Unified Approach to data Security look like?
At the core of the unified approach is a unified policy platform that applies the zero trust principle to to secure access and protect data across silos using attribute-based policies.
Key elements of the platform include:
Data-Centric Security
An approach to safeguarding sensitive information by protecting the data itself with real-time enforcement.
Zero Trust Architecture
A cybersecurity model designed to secure resources by eliminating implicit trust and verifying every stage of a digital interaction.
Dynamic Authorization
Enforce zero trust data-centric security controls in real-time, using policy to ensure least privilege access and safeguard data.
Centralized Policy Management
Unified policy platform that secures access and protects data across silos using attribute-based policies
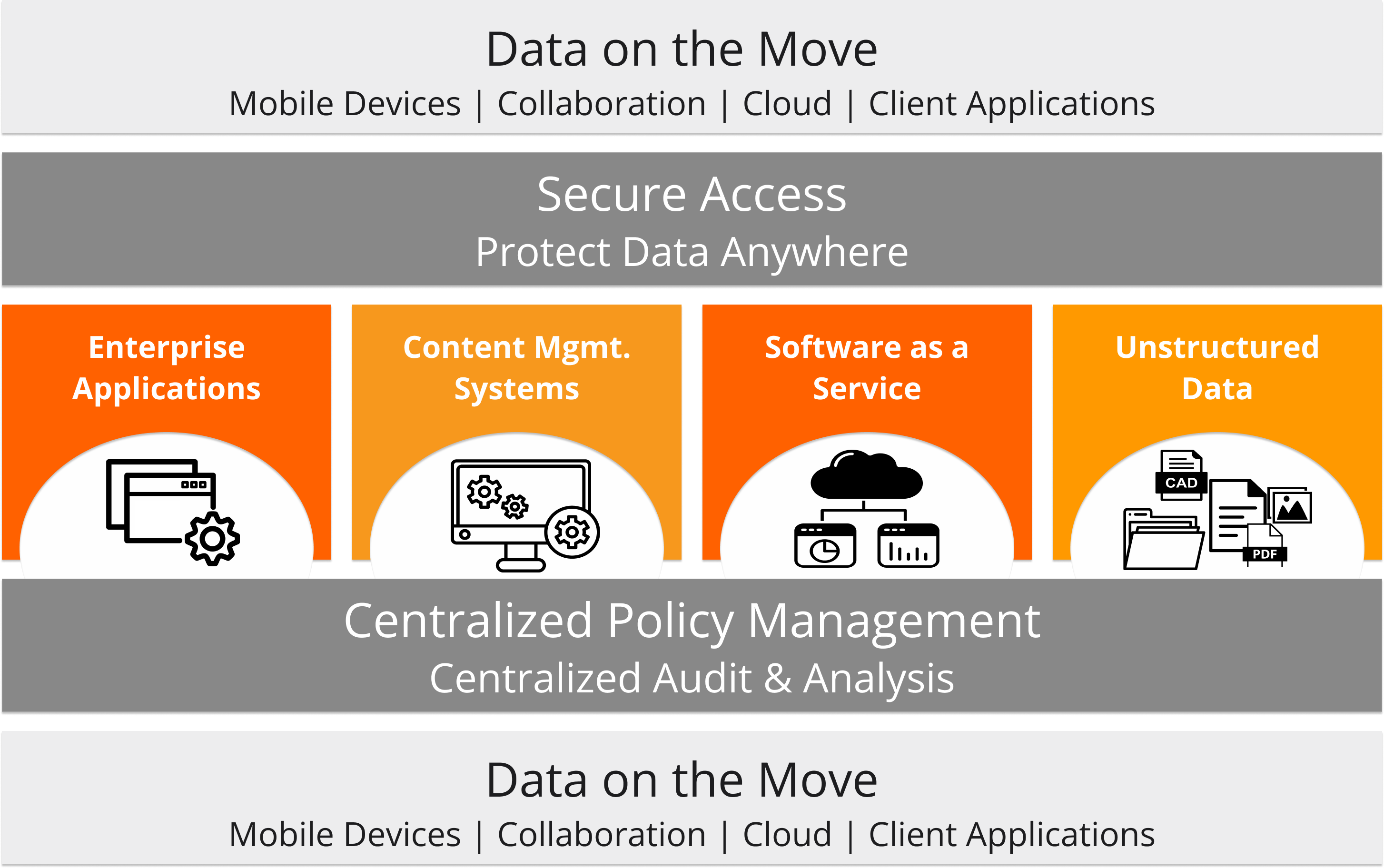
Automation
Automates data security, compliance procedures, and internal controls to enhance competitiveness and agility.
Integration
Out-of-the-box integration with apps, microservices, and business processes without disruptions.
Enforcement
Detects, alerts and applies preventive controls to enforce policy in real time.
Deployment
Runs in cloud natively, deploys using containers in a hybrid and multi-cloud environments.
CloudAz: A unified policy Platform
CloudAz is a unified policy platform with real-time enforcement that centralizes administration and employs a zero trust strategy to enforce data-centric security measures and compliance in real time, by automating least privilege access and securing applications and data.

CloudAz Features
Unify & Modernize it
Streamline IT infrastructure, unify application and business services under a shared services model, expedite system consolidation and eliminate security silos, accelerate cloud adoption without compromising security coverage and total cost of ownership.
Ensure Compliance
Ensure compliance with regulations such as GDPR, ITAR, SOX and EH&S, simplify audit processes with centralized logging and reporting of all data access activity and authorization decisions.
Improve Business Agility
Accelerate time to market and enhance competitive advantage through automation and simplified change management; easily incorporate new business models without code changes and application downtime.
Enhance Cybersecurity
Prevent data leakage and cyber-attacks by automating least privilege access to eliminate implicit trust and safeguard data across business-critical applications (e.g. SAP, Siemens, Microsoft, ServiceNow, Oracle), whether the data is at rest or on the move.
Increase Collaboration
Safeguard trade secrets and sensitive information to ensure secure data sharing and accelerate collaboration through central access control and data segregation policies.
Data-Centric Security Enforcement
CloudAz is the control center of the NextLabs comprehensive Data centric Security Software Suite, which includes three enforcement solutions to protect data at the source (Application Enforcer), persistently protect files at rest and on the move (SkyDRM), and control global data access (Data Access Enforcer).
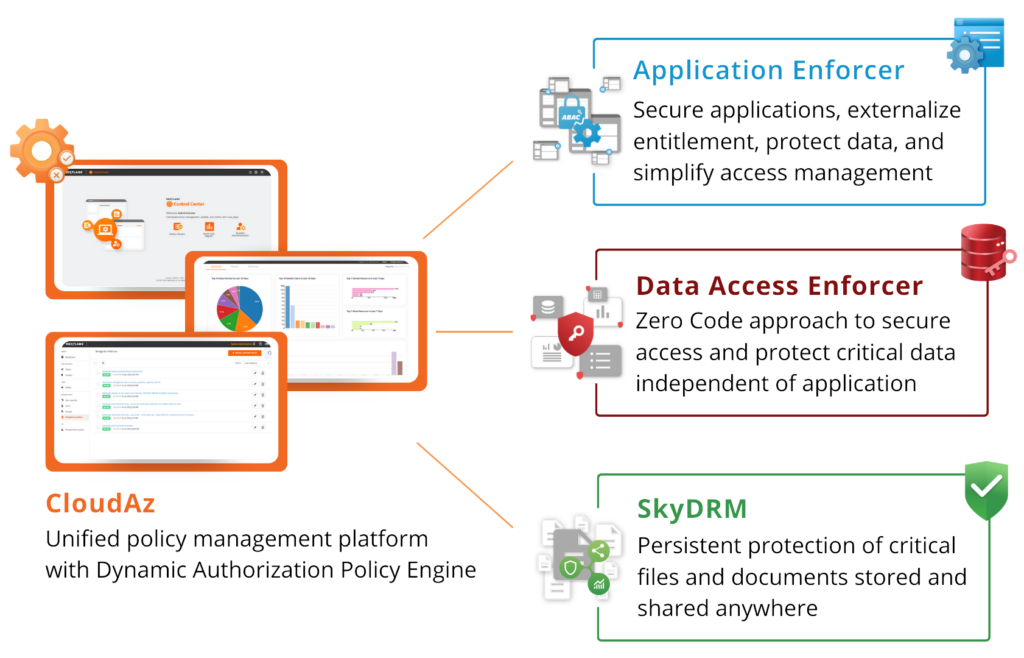
CloudAz can be deployed anywhere, be it on-premises, in private cloud, or as a SaaS. CloudAz runs natively on AWS, Azure, OpenShift and Google Cloud. With support for multiple deployment models, it gives you the freedom to choose the right cloud deployment strategy, whether it is hybrid or multi-cloud. With the ability to create new instances across multiple landscapes – set up development, test, and production environments can be done quickly. Policies can be transported between cloud and on-premise deployments, ensuring consistent policy enforcement across all environments.